Posts tagged "Security"
-
The Next.js and React teams have disclosed twelve security vulnerabilities: one in React Server Components and eleven in Next.js, all patched on May 6, 2026, plus a follow-up advisory on May 7. The issues span middleware/proxy bypass, cross-site scripting (XSS), server-side request forgery (SSRF), cache poisoning, and denial of service (DoS). No detailed proof-of-concept information has been published. Here’s what Netlify customers need to know.
Summary
If you run Next.js on Netlify, we strongly recommend upgrading
nextto 15.5.18 or 16.2.6 and redeploying. This also brings in the patched React Server Components dependency. Projects using Pages Router with i18n and Next.js Middleware / Proxy also need OpenNext Netlify Next.js adapter v5.15.11. If you usereact-server-dom-*outside of Next.js, upgrade to 19.0.6 / 19.1.7 / 19.2.6 matching your React minor. See What should I do? for full steps.Netlify’s platform is not vulnerable to several of these CVEs. Image Optimization, WebSocket SSRF, RSC cache poisoning, and the cache-poisoned-redirect bypass do not affect Netlify projects. See Impact on Netlify for the per-CVE verdict.
Vulnerabilities
React (
react-server-dom-*)This affects
react-server-dom-webpack,react-server-dom-parcel, andreact-server-dom-turbopack. The Next.js advisory GHSA-8h8q-6873-q5fj tracks the same issue downstream.Vulnerability Severity Affected versions Fixed in GHSA-rv78-f8rc-xrxh — DoS in Server Components (CVE-2026-23870) High 19.0.0–19.0.5, 19.1.0–19.1.6, 19.2.0–19.2.5 19.0.6, 19.1.7, 19.2.6 Next.js
All Next.js issues are patched in 15.5.18 and 16.2.6. Earlier minors of 15.x and 16.x will not be patched; affected projects must upgrade to a patched minor.
Vulnerability Severity Affected versions GHSA-8h8q-6873-q5fj — DoS with Server Components High ≥13.0.0 GHSA-267c-6grr-h53f — Middleware / Proxy bypass in App Router via segment-prefetch routes High ≥15.2.0 GHSA-26hh-7cqf-hhc6 — Follow-up to GHSA-267c-6grr-h53f: incomplete fix for middleware.tswith TurbopackHigh ≥15.2.0 GHSA-mg66-mrh9-m8jx — DoS via connection exhaustion in apps using Cache Components High ≥15.0.0 (apps using Cache Components) GHSA-492v-c6pp-mqqv — Middleware / Proxy bypass through dynamic route parameter injection High ≥15.4.0 GHSA-c4j6-fc7j-m34r — SSRF in applications using WebSocket upgrades High ≥13.4.13 GHSA-36qx-fr4f-26g5 — Middleware / Proxy bypass in Pages Router applications using i18n High ≥12.2.0 GHSA-ffhc-5mcf-pf4q — XSS in App Router applications using CSP nonces Medium ≥13.4.0 GHSA-gx5p-jg67-6x7h — XSS in beforeInteractivescripts with untrusted inputMedium ≥13.0.0 GHSA-h64f-5h5j-jqjh — DoS in the Image Optimization API Medium ≥10.0.0 GHSA-wfc6-r584-vfw7 — Cache poisoning in React Server Component responses Medium ≥14.2.0 GHSA-vfv6-92ff-j949 — Cache poisoning via collisions in React Server Component cache-busting Low ≥13.4.6 GHSA-3g8h-86w9-wvmq — Middleware / Proxy redirects can be cache-poisoned Low ≥12.2.0 Impact on Netlify
Denial of service
GHSA-8h8q-6873-q5fj and GHSA-mg66-mrh9-m8jx are server-side denial-of-service (DoS) vulnerabilities. On Netlify, these have minimal impact: our autoscaling serverless architecture means that a malicious request resulting in a crashed or hung function does not affect other requests. However, active exploitation could increase your function costs. Note that Cache Components (GHSA-mg66-mrh9-m8jx) is an opt-in Next.js feature that is not enabled by default. Upgrading Next.js resolves both.
GHSA-h64f-5h5j-jqjh affects the Next.js Image Optimization API. Netlify projects are not affected: this Next.js code path is not used on Netlify — image optimization is handled by Netlify Image CDN, a separate service that runs outside your project’s functions with its own protections against this class of issue.
Middleware / proxy bypass
These four CVEs affect Next.js middleware and proxy routing. Because Netlify runs Next.js middleware via our own edge function adapter, the impact varies per CVE:
- GHSA-3g8h-86w9-wvmq (cache-poisoned redirects): Netlify projects are not affected. Our OpenNext Netlify Next.js adapter already varies cached responses on the
x-nextjs-dataheader. - GHSA-492v-c6pp-mqqv (dynamic route parameter injection): Netlify projects are affected, and the upstream Next.js fix applies. Upgrading Next.js resolves the issue.
- GHSA-36qx-fr4f-26g5 (Pages Router i18n bypass): Netlify projects using Pages Router with i18n and Next.js Middleware / Proxy are affected. The upstream Next.js patch alone does not resolve this on Netlify; a Netlify-specific fix shipped in OpenNext Netlify Next.js adapter v5.15.11. See how to upgrade below.
- GHSA-267c-6grr-h53f (App Router segment-prefetch bypass) and GHSA-26hh-7cqf-hhc6 (follow-up): Netlify projects are affected, and the upstream Next.js fix applies. Upgrading Next.js resolves both.
Cross-site scripting
GHSA-ffhc-5mcf-pf4q and GHSA-gx5p-jg67-6x7h are client-side XSS vulnerabilities. Regardless of hosting provider, all apps using CSP nonces in App Router or passing untrusted input to
beforeInteractivescripts may be vulnerable. Upgrade Next.js to remediate.Server-side request forgery
GHSA-c4j6-fc7j-m34r affects applications using WebSocket upgrades. Netlify projects are not affected: Netlify Functions and Edge Functions do not support WebSocket upgrades, so this Next.js code path cannot be exercised on Netlify.
Cache poisoning
GHSA-wfc6-r584-vfw7 and GHSA-vfv6-92ff-j949 affect React Server Component response caching. Netlify projects are not affected: Netlify’s CDN does not rely on the
_rsccache-busting query parameter (so collisions in it cannot poison cache entries), and it honorsVaryon RSC-related request headers.What should I do?
We strongly recommend upgrading as soon as possible to patched releases:
- Next.js projects: upgrade
nextto 15.5.18 or 16.2.6. This bundles the patched React Server Components dependency, so a separatereact-server-dom-*upgrade is not needed. - Direct
react-server-dom-*users (React Router RSC, Vite RSC plugin, custom RSC setups): upgradereact-server-dom-webpack,react-server-dom-parcel, orreact-server-dom-turbopackto 19.0.6, 19.1.7, or 19.2.6 — matching your React minor.
For Next.js 13.x and 14.x users: patches are not planned for these versions. Consider upgrading to Next.js 15.x or 16.x.
For projects using Pages Router with i18n and Next.js Middleware / Proxy (GHSA-36qx-fr4f-26g5), the upstream Next.js fix does not fully apply on Netlify. The fix ships in OpenNext Netlify Next.js adapter v5.15.11:
- Auto-installed adapter (default): redeploy.
- Manually installed adapter: upgrade
@netlify/plugin-nextjsto v5.15.11 and redeploy. We recommend not pinning the adapter version so future fixes ship automatically.
Note that any publicly available deploy previews and branch deploys may remain vulnerable until they are automatically deleted. Consider deleting these deploys manually.
Resources
- GHSA-3g8h-86w9-wvmq (cache-poisoned redirects): Netlify projects are not affected. Our OpenNext Netlify Next.js adapter already varies cached responses on the
-
Team Owners can now guarantee that projects stay within the team to meet compliance or ownership requirements by blocking every project from being transferred to another team.
Once a Team Owner blocks project transfers out of the team, even the Team Owner cannot transfer projects out of the team unless they change this setting, which is tracked in the team’s audit log.
Try it out
To change the setting, go to Team settings > Access & security > Transfer site settings and select Edit settings.
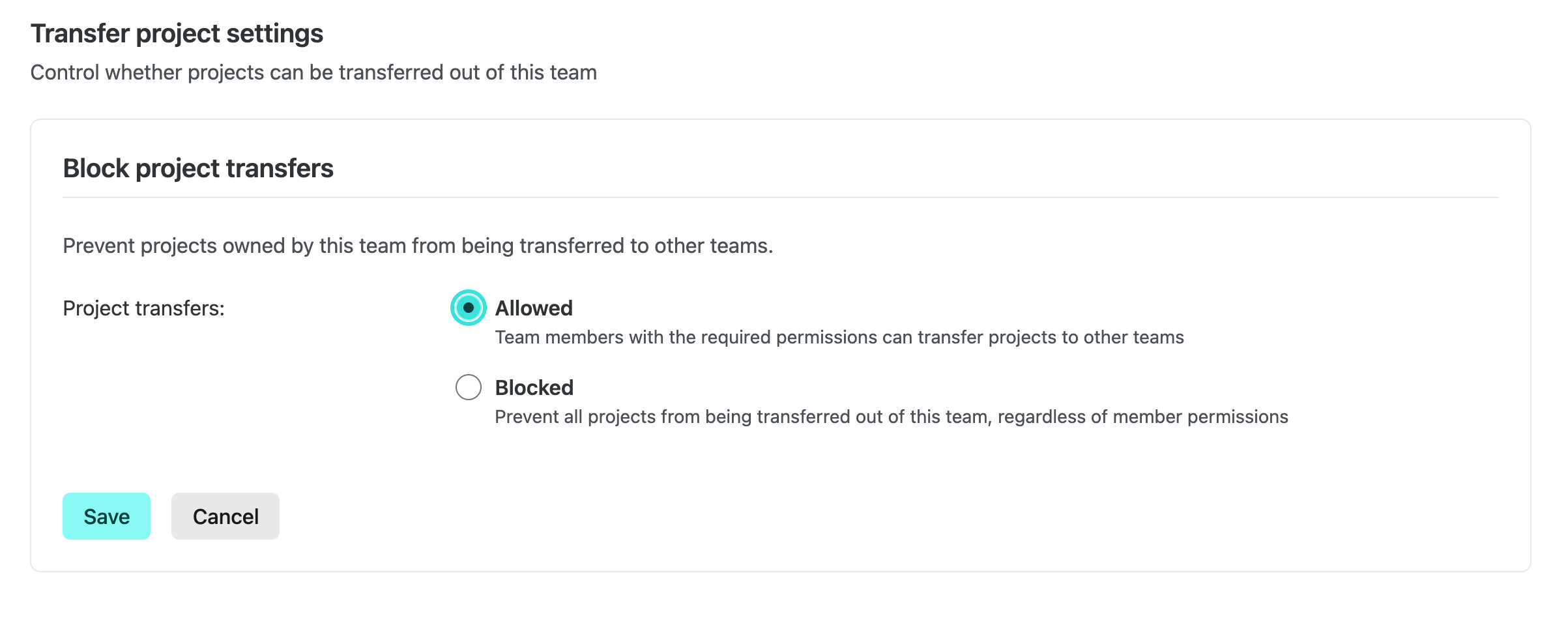
When transfers are blocked, the Transfer project action is hidden for every project owned by the team and the backend rejects transfer requests for those projects.
Enterprise defaults
Enterprise teams start with project transfers set to Blocked for security reasons, but Team Owners can change this setting to Allowed at any time. Only Team Owners can change this setting and changes are recorded in the team audit log.
Learn more
Learn more in our docs on Transferring a project.
-
A denial-of-service (DoS) vulnerability (CVE-2026-23869, CVSS 7.5) has been disclosed affecting React Server Components (RSCs), a feature used by Next.js and other React metaframeworks. A malicious payload can cause excessive CPU consumption. Here’s what Netlify customers need to know.
Impact on Netlify
Nominally, this is a server-side DoS vulnerability. However, on Netlify this has minimal impact: our autoscaling serverless architecture means that a malicious request resulting in a crashed or hung function does not affect other requests. However, active exploitation could increase your function costs.
Affected frameworks
All RSC frameworks are affected:
- Next.js (see version table below)
- React Router 7 (if using RSC preview)
- Waku
@parcel/rsc@vitejs/plugin-rsc
Astro, Gatsby, and Remix are not affected.
React affected versions
See the React advisory for full details.
Affected versions Fixed in 19.0.0–19.0.4 19.0.5 19.1.0–19.1.5 19.1.6 19.2.0–19.2.4 19.2.5 Next.js affected versions
See the Next.js advisory for full details.
Affected versions Fixed in 13.3.0+ EOL - no fix 14.x EOL - no fix 15.0.0–15.5.14 15.5.15 16.0.0–16.2.2 16.2.3 What should I do?
If any of your projects are using an affected version, we recommend upgrading as soon as possible to a patched release.
For Next.js 13.x and 14.x users: patches are not planned for these versions. Consider upgrading to Next.js 15.x or 16.x.
Note that any publicly available deploy previews and branch deploys may remain vulnerable until they are automatically deleted. Consider deleting these deploys manually.
Resources
-
Netlify now automatically blocks bot scans targeting PHP paths across all plans — no configuration required.
Previously, these bots generated noise in Observability logs and metrics. They showed up without a
User-Agentheader. Netlify now blocks them at the edge.Since rolling out edge-level blocking on December 28, 2025, Netlify has blocked 2.9 billion of these requests.
-
A denial-of-service (DoS) vulnerability (CVE-2026-23864, CVSS 7.5) has been disclosed affecting React Server Components (RSCs), a feature used by Next.js and other React metaframeworks. A malicious payload can cause memory exhaustion or excessive CPU consumption. Next.js has also disclosed two unrelated medium-severity CVEs (CVE-2025-59471, CVE-2025-59472) patched in the same releases. Here’s what Netlify customers need to know.
Impact on Netlify
Nominally, this is a server-side DoS vulnerability. However, on Netlify this has minimal impact: our autoscaling serverless architecture means that a malicious request resulting in a crashed or hung function does not affect other requests. However, active exploitation could increase your function costs.
Affected frameworks
All RSC frameworks are affected:
- Next.js (see version table below)
- React Router 7 (if using RSC preview)
- Waku
@parcel/rsc@vitejs/plugin-rsc
Astro, Gatsby, and Remix are not affected.
React affected versions
See the React blog post for full details.
Affected versions Fixed in 19.0.0–19.0.3 19.0.4 19.1.0–19.1.4 19.1.5 19.2.0–19.2.3 19.2.4 Next.js affected versions
See the Next.js advisory for full details.
Affected versions Fixed in 13.3.0+ EOL - no fix 14.x EOL - no fix 15.0.0–15.0.7 15.0.8 15.1.0–15.1.10 15.1.11 15.2.0–15.2.8 15.2.9 15.3.0–15.3.8 15.3.9 15.4.0–15.4.10 15.4.11 15.5.0–15.5.9 15.5.10 15.x canaries 15.6.0-canary.61 16.0.0–16.0.10 16.0.11 16.1.0–16.1.4 16.1.5 16.x canaries 16.2.0-canary.9 What should I do?
If any of your projects are using an affected version, we recommend upgrading as soon as possible to a patched release.
For Next.js 13.x and 14.x users: patches are not planned for these versions. Consider upgrading to Next.js 15.x or 16.x.
Note that any publicly available deploy previews and branch deploys may remain vulnerable until they are automatically deleted. Consider deleting these deploys manually.
Resources
-
The React Router team has disclosed six security vulnerabilities affecting React Router and Remix. Here’s what Netlify customers need to know.
Vulnerabilities
Vulnerability Remix versions React Router versions & modes CVE-2025-61686 - Path traversal ≤2.17.1 7.0.0–7.9.3
All modesCVE-2025-68470 - Open redirect - 6.0.0–6.30.1, 7.0.0–7.9.5
All modesCVE-2026-22030 - CSRF ≤2.17.2 7.0.0–7.11.0
Framework onlyCVE-2025-59057 - Meta XSS 1.15.0–2.17.0 7.0.0–7.8.2
Framework onlyCVE-2026-22029 - Redirect XSS ≤2.17.3 6.0.0–6.30.2, 7.0.0–7.11.0
Framework, DataCVE-2026-21884 - ScrollRestoration XSS ≤2.17.2 7.0.0–7.11.0
Framework onlyImpact on Netlify
CVE-2025-61686 (path traversal)
This vulnerability affects
@react-router/node,@remix-run/node, and@remix-run/deno. These packages are not used on Netlify, therefore Netlify projects are not affected.CVE-2025-68470 (open redirect)
Apps with unsafe uses of React Router navigation APIs may be hijacked to redirect to arbitrary origins.
Regardless of hosting provider, all apps constructing paths from untrusted user input may be vulnerable.
CVE-2026-22030 (CSRF)
Actions and experimental RSC Server Functions can be triggered by cross-origin form submissions, allowing an attacker to execute actions on behalf of authenticated users.
Regardless of hosting provider, all apps may be vulnerable.
CVE-2025-59057, CVE-2026-22029, and CVE-2026-21884 (XSS)
These are cross-site scripting (XSS) vulnerabilities. For example, in CVE-2026-22029 actions and experimental RSC Server Functions performing a redirect to a path constructed from untrusted user input may be hijacked to execute arbitrary JavaScript in the browser.
Regardless of hosting provider, all apps passing untrusted data into certain APIs may be vulnerable. (The Remix team has left this intentionally vague.)
What should I do?
If any of your projects are using any affected version listed above, we strongly recommend upgrading as soon as possible to patched releases:
react-router7.12.0 or later (for React Router 7.x)react-router6.30.2 or later (for React Router 6.x)@remix-run/react2.17.4 or later@remix-run/server-runtime2.17.4 or later
Note that any publicly available deploy previews and branch deploys may remain vulnerable until they are automatically deleted. Consider deleting these deploys manually.
-
The Node.js team has released a security update addressing a denial-of-service vulnerability affecting applications that use
async_hooks(including in dependencies). Here’s what Netlify customers need to know.Vulnerability
When
async_hooksare enabled on certain versions of Node.js, a stack overflow causes the Node.js process to exit immediately rather than throw a catchable error. This bypassestry-catchblocks and uncaught exception handlers entirely.A malicious actor could send a crafted payload to crash a server.
Note that many common tools and frameworks use
async_hooksunder the hood, notably APM and tracing tools (e.g. DataDog, NewRelic, OpenTelemetry) as well as Next.js App Router and other React Server Components implementations. You can find more details on that here.Impact on Netlify
This is a server-side denial-of-service (DoS) vulnerability. On Netlify, this has minimal impact: our autoscaling serverless architecture means that a malicious request resulting in a crashed or hung function does not affect other requests. However, active exploitation could increase your cold starts and your function costs.
Note that Node.js used during your project’s build is not impacted at all.
What should I do?
If you have opted your Netlify Functions into Node.js 18, we recommend upgrading to Node.js 20 or later. Node.js 18 reached end-of-life in April 2025 and thus will not be patched.
Otherwise, there is no action for you to take. Although this CVE’s impact to Netlify sites is limited, deployed Netlify Functions will be updated to patched Node.js versions automatically on a rolling basis.
For completeness, please note that the Node.js version used during your project’s build is not relevant to this CVE. There is no action for you to take and this will not be automatically patched.
Resources
-
The Svelte team has disclosed five CVEs affecting the Svelte and SvelteKit ecosystem. Here’s what Netlify customers need to know.
Vulnerabilities
- CVE-2026-22775: Memory/CPU exhaustion in
devalue(5.1.0–5.6.1) - CVE-2026-22774: Memory exhaustion in
devalue(5.3.0–5.6.1) - CVE-2026-22803: Server crash in
@sveltejs/kit(2.49.0–2.49.4) - CVE-2025-67647: Server crash and SSRF in
@sveltejs/kit(2.44.0–2.49.4) and@sveltejs/adapter-node(2.19.0–2.49.4) - CVE-2025-15265: XSS in
svelte(5.46.0–5.46.3)
Impact on Netlify
CVE-2026-22775, CVE-2026-22774, and CVE-2026-22803
These are server-side denial-of-service (DoS) vulnerabilities. On Netlify, these have minimal impact: our autoscaling serverless architecture means that a malicious request resulting in a crashed or hung function does not affect other requests. However, active exploitation could increase your function costs.
In addition, note that only sites using the experimental Remote Functions feature are affected.
CVE-2025-67647
As above, this DoS vulnerability involves intentionally “crashing” a server. On Netlify, this has minimal impact.
The SSRF vulnerability affects a
@sveltejs/adapter-node, which is not used by apps deployed to Netlify.CVE-2025-15265
This is a client-side cross-site scripting (XSS) vulnerability. Regardless of hosting provider, all apps using the experimental
hydratablewith unsanitized user-controlled keys are vulnerable.What should I do?
Although the impact to Netlify sites is limited in this case, we always strongly recommend upgrading as soon as possible to patched releases:
devalue5.6.2 or later@sveltejs/kit2.49.5 or later@sveltejs/adapter-node5.5.1 or latersvelte5.46.4 or later
Resources
- CVE-2026-22775: Memory/CPU exhaustion in
-
Update (2025-12-12 00:41 UTC): The React and Next.js patches initially published on Dec. 11 at 21:10 incompletely addressed the vulnerabilities. A follow-up CVE was issued and follow-up patches have been released by the React and Next.js teams. All versions below have been updated accordingly. If you upgraded during this 3.5-hour window, please upgrade again.
Following last week’s critical vulnerability in React and Next.js, two additional vulnerabilities are being publicly disclosed today:
- CVE-2025-55184: Denial of Service (CVSS 7.5/10, high severity)
- A malicious actor can send a request that makes the Next.js server hang.
- On Netlify, this type of request gets interrupted by a timeout after 30–40 seconds. As Next.js on Netlify runs on automatically scaled serverless functions, there is no risk of impact to legitimate requests. However, this can have impacts to your monthly bill due to increased bandwidth and function CPU usage.
- CVE-2025-55183: Leaking Server Functions (CVSS 5.3/10, medium severity)
- A malicious actor can send a request that leaks the compiled body of a given Server Function/Action.
Impact
In both cases, all Next.js sites using App Router are vulnerable. This includes all v14 releases up to and including 14.2.33, all v15 releases up to and including 15.5.7, all v16 releases up to and including 16.0.8, and v13.4+ if opted into the
experimental.serverActionsflag. (In the case of CVE-2025-55183, only sites actually using any Server Actions are vulnerable.)We have collaborated with the React and Next.js teams to roll out mitigations to the Netlify network in advance of public disclosure.
However, as we’ve seen in the past week, malicious actors around the world are constantly working to quickly identify novel ways to exploit newly published vulnerabilities. The best protection is to upgrade.
What should I do?
Upgrade as soon as possible. Both vulnerabilities are patched in all these releases:
- Next.js 14.2.35
- Next.js 15.0.7, 15.1.11, 15.2.8, 15.3.8, 15.4.10, or 15.5.9
- Next.js 16.0.10
As Next.js 13 has been unsupported for over a year, the Next.js team has chosen not to patch it. If your site uses Next.js 13.4+ and has opted in to the
experimental.serverActionsflag, we strongly recommend upgrading to 14.2.34 or later as soon as possible (note: v14 is also technically unsupported).To be abundantly clear: if you have upgraded to address last week’s CVE, you must upgrade once again.
Other RSC frameworks
These are React vulnerabilities, in the React Server Functions protocol present in all versions of React 19 up to and including 19.2.1.
The following RSC implementations are therefore vulnerable:
waku,@parcel/rsc,@vitejs/plugin-rsc,react-server-dom-parcel,react-server-dom-webpack,react-server-dom-turbopack, and the React Router 7 RSC preview.If you are using any of these, upgrade it to the latest version and upgrade
reactto 19.0.3, 19.1.4, or 19.2.3 as soon as possible.Resources
We are working continually with the React and Next.js teams and are committed to keeping your sites secure on Netlify.
This post was last updated on 2025-12-11 at 21:15 UTC
- CVE-2025-55184: Denial of Service (CVSS 7.5/10, high severity)